Heartbleed in plain English
It’s not a virus, it’s a bug in those URLs with the image of a little lock. Read on and understand what happened if you are not a techie.
When we connect to the web to reach some websites such as social network, email, instant messaging (IM) and some virtual private networks (VPNs), we transfer financial and sensitive data. Most of the time there is a lock: you see the URL starting with https:// meaning that all the data travels in an encrypted form.
One of the most famous cryptography software currently in use is OpenSSL.
“They broke the Internet”
This bug was independently discovered by a team of security engineers, from Codenomicon and Google Security on 7th April and fixed the same day with a patch. In a few hours many web services providers using OpenSSL implemented the patch. But nobody knows what information were previously leaked.
What is Heartbleed by example
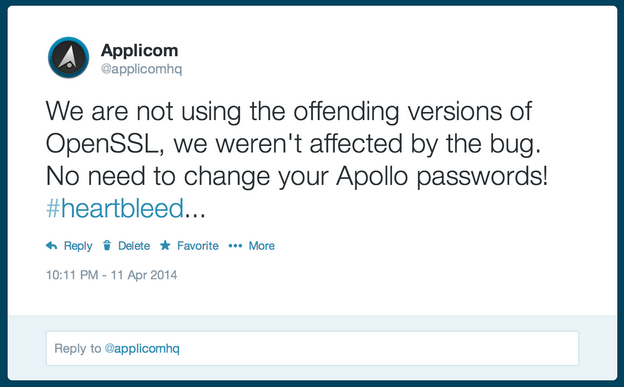
Heartbleed is a bug affecting only some versions of the OpenSSL software. Because of this bug an attacker was able to access small portions of the server RAM memory leaving no traces showing the cyber-attack was performed.
What does happen to those RAM memories when attacked exploiting the Heartbleed bug?
It depends, it could be random memory garbage worth nothing, or it could be data about a web request being served at that moment by the web server. In the latter case, an attacker could gain valuable informartion like the authentication cookie of that user, and impersonate her on that website.
The fact that the attack doesn’t leave any trace, and it’s repeatable at will on a target server, is the reason why this has been correctly labeled, by many, as one of the worst security problem ever happened on the Internet!
In practice: All the pre-7th, April OpenSSL communications may be potentially compromised.
ID Session: do you log-out after using your email/social networks?
The average user log-in to a service, like Pinterest, remaining logged for days, even for weeks. Why is that not advisable? Because if someone got our ID Session number, by the Heartbleed bug, he can enter our account till we don’t log-out and makes that ID Session number ineffective. So, after your businesses, always log-out!
Password: how often do you clean your house?
With the same frequency people usually change their password. Hearthbleed could have been the door to get our password or other sensitive information. That is why most of us received an email advising to kindly change our passwords (Pinterest was not just a random example ;) ).
What about my bank accounts?
Many banks sent this kind of suggesting emails and those using the OpenSSL technology already updated the patch. Besides that they usually have additional layers of security that makes more difficult to breach in.
More to know
“Exploitation of this bug does not leave any trace of anything abnormal happening to the logs.” - http://heartbleed.com/
The OpenSSL core team is ridiculously small: only four people. https://www.openssl.org/about/ Consider this technology is being in use by gigantic companies.
Anyway, for those who want to sustain their part-time activity here is the donation link: https://www.openssl.org/support/donations.html
The NSA denied the accusation claiming they have known and maybe exploited the bug for about two years. http://www.bloomberg.com/video/what-and-when-did-nsa-know-about-heartbleed-bug-CcNm~m5ZSzC9GWx4na6L2Q.html
